Search Site Server Scanner - ATSCAN v6.2
Description:
- SEARCH engine
- XSS scanner.
- Sqlmap.
- LFI scanner.
- Filter wordpress and Joomla sites in the server.
- Find Admin page.
- Decode / Encode MD5 + Base64.
- Ports scan.
- Scan E-mails in sites.
- Use proxy.
- Random user agent.
- Fandom search engine.
- Scan errors.
- Detect Cms.
- Multiple instant scan.
- Disponible on BlackArch Linux Platform.
Libreries to install:
ap-get install libxml-simple-perl
aptitude install libio-socket-ssl-perl
aptitude install libcrypt-ssleay-perl
NOTE: Works in linux platforms. Best Run on Ubuntu 14.04, Kali Linux 2.0, Arch Linux, Fedora Linux, Centos | if you use a windows you can download manualy.
Download & Executution:
git clone https://github.com/AlisamTechnology/ATSCAN
cd ATSCAN
chmod +x ATSCAN
OR
$chmod +x atscan.pl
Execute: perl ./atscan.pl
Help: perl ./atscan.pl --help
Update: perl ./atscan.pl --update
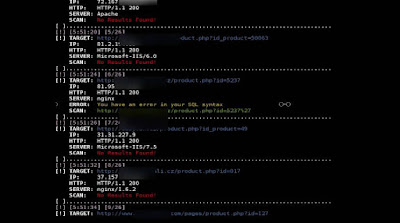
Screenshots:
Help:
--proxy
Set tor proxy [Ex: socks://localhost:9050]
--dork
dork to search [Ex: house,cars,hotel]
--level
Scan level (+- Number of page results to scan)
--xss
Xss scan
--joomrfi
joomla local file inclusion scan
-t
Target
--TARGET
Captured Target
--FULL_TARGET
Captured Full Target
--exp
Set exploit
--valid
Text to validate results
--sqlmap
Sqlmaping xss results
--lfi
local file inclusion
--joomrfi
get joomla sites with rfi
--shell
shell link [Ex: http://www.site.com/shell.txt ]
--wpadf
get wordpress sites with arbitery file download
--admin
get site admin page
--shost
get site subdomains
--ports
scan server ports
--start
start scan port
--end
end scan port
--all
complete mode
--basic
basic mode
--select
Select mode you can set rang of ports
--sites
sites in the server
--wp
get wordpress sites
--joom
Getjoomla sites
--upload
get sites with upload files
--zip
get sites with zip files
--save
file prefix to save results (if not set tool sets one)
--md5
convert to md5
--encode64
encode base64 string
--decode64
decode base64 string
--isup
check http status 200
Extract e-mails
--command
External Command
--replace
string to replace
--with
string to replace with
--save
Set prefix to saved files
--rang
Set range of ip
--nobanner
Hide tool banner
--beep
Produce beep sount if positive scan found
Examples:
Simple search:
Search: --dork [dork] --level [level]
Search with many dorks: --dork [dork1,dork2,dork3] --level [level]
Search + set save file: --dork [dorks.txt] --level [level] --save myfile.txt
Search + Replace + Exploit: --dork [dorks.txt] --level [level] --replace [string] --with [string] --valid [string]
Search + Extract e-mails: --dork [dorks.txt] --level [level] --email
Subscan from Serach Engine:
Search + Exploitation: --dork [dork] --level [10] --xss/--lfi/--wp ...
Search + xss + sqlmap: --dork [dork] --level [10] --xss --sqlmap
Search + Server Exploitation: -t [ip] --level [10] --xss/--lfi/--wp ...
Search + Server Exploitation: --rang 133.21.10.155-19.102.25.14 --level [10] --xss/--lfi/--wp ...
Search + Replace + Exploit: --dork [dork] --level [10] --replace [string] --with [string] --exp [exploit] --xss/--lfi/--wp ...
Validation:
Search + Exploit + Validation: --dork [dork] --level [10] --exp --isup/--valid [string]
Search + Server Exploit + Validation: -t [ip] --level [10] --exp --isup/--valid [string]
Search + Replace + Exploit: --dork [dork] --level [10] --replace [string] --with [string] --isup/--valid [string]
Use List / Target:
-t [target/targets.txt] --exp --isup/--valid [string]
-t [target/targets.txt] --xss/--lfi ..
Server:
Get Server sites: -t [ip] --level [value] --sites
Get Server wordpress sites: -t [ip] --level [value] --wp
Get Server joomla sites: -t [ip] --level [value] --joom
Get Server upload sites: -t [ip] --level [value] --upload
Get Server zip sites files: -t [ip] --level [value] --zip
WP Arbitry File Download: -t [ip] --level [value] --wpadf
Joomla RFI: -t [ip] --level [1] --joomfri --shell [shell link]
Scan basic tcp (quick): -t [ip] --ports --basic tcp
Scan basic udp basic (quick): -t [ip] --ports --basic udp
Scan basic udp+tcp: -t [ip] --ports --basic udp+tcp
Scan complete tcp: -t [ip] --ports --all tcp
Scan complete udp: -t [ip] --ports --all udp
Scan complete udp+tcp: -t [ip] --ports --all udp+tcp
Scan rang tcp: -t [ip] --ports --select tcp --start [value] --end [value]
Scan rang udp: -t [ip] --ports --select udp--start [value] --end [value]
Scan rang udp + tcp: -t [ip] --ports --select udp+tcp --start [value] --end [value]
Encode / Decode:
Generate MD5: --md5 [string]
Encode base64: --encode64 [string]
Decode base64: --decode64 [string]
External Command:
--dork [dork/dorks.txt] --level [level] --command "curl -v --TARGET"
--dork [dork/dorks.txt] --level [level] --command "curl -v --FULL_TARGET"
-t [target/targets.txt] --level [level] --command "curl -v --TARGET"
-t [target/targets.txt] --command "curl -v --FULL_TARGET"
Multiple Scan:
--dork [dork] --level [10] --xss/--lfi/--wp ...
--dork [dork] --level [10] --replace [string] --with [string] --exp [exploit] --xss --lfi --wp ...
-t [ip] --level [10] --xss --lfi --wp ...
-t [targets] --xss --lfi --wp ...