Sudomy
Kang Asu
Sudomy - Subdomain Enumeration & Analysis
Sudomy is a subdomain enumeration tool, created using a bash script, to analyze domains and collect subdomains in fast and comprehensive way.
Features
For recent time, Sudomy has these 9 features:
- Easy, light, fast and powerful. Bash script is available by default in almost all Linux distributions. By using bash script multiprocessing feature, all processors will be utilized optimally.
- Subdomain enumeration process can be achieved by using active method or passive method
- Active Method
- Sudomy utilize Gobuster tools because of its highspeed performance in carrying out DNS Subdomain Bruteforce attack (wildcard support). The wordlist that is used comes from combined SecList (Discover/DNS) lists which contains around 3 million entries
- Passive Method
- By selecting the third-party sites, the enumeration process can be optimized. More results will be obtained with less time required. Sudomy can collect data from these well-curated 16 third-party sites:
https://dnsdumpster.com
https://web.archive.org
https://shodan.io
https://virustotal.com
https://crt.sh
https://www.binaryedge.io
https://securitytrails.com
https://sslmate.com/certspotter
https://censys.io
https://threatminer.org
http://dns.bufferover.run
https://hackertarget.com
https://www.entrust.com/ct-search/
https://www.threatcrowd.org
https://riddler.io
https://findsubdomains.com
- By selecting the third-party sites, the enumeration process can be optimized. More results will be obtained with less time required. Sudomy can collect data from these well-curated 16 third-party sites:
- Active Method
- Test the list of collected subdomains and probe for working http or https servers. This feature uses a third-party tool, httprobe.
- Subdomain availability test based on Ping Sweep and/or by getting HTTP status code.
- The ability to detect virtualhost (several subdomains which resolve to single IP Address). Sudomy will resolve the collected subdomains to IP addresses, then classify them if several subdomains resolve to single IP address. This feature will be very useful for the next penetration testing/bug bounty process. For instance, in port scanning, single IP address won’t be scanned repeatedly
- Performed port scanning from collected subdomains/virtualhosts IP Addresses
- Testing Subdomain TakeOver attack
- Taking Screenshotsof subdomains
- Report output in HTML or CSV format
How Sudomy Works
Sudomy is using cURL library in order to get the HTTP Response Body from third-party sites to then execute the regular expression to get subdomains. This process fully leverages multi processors, more subdomains will be collected with less time consumption.
Comparison
The following are the results of passive enumeration DNS testing of Sublist3r, Subfinder, and Sudomy. The domain that is used in this comparison is bugcrowd.com.
| Sudomy | Subfinder | Sublister |
|---|---|---|
Asciinema :
Installation
Sudomy is currently extended with the following tools. Instructions on how to install & use the application are linked below.
| Tools | License | Info |
|---|---|---|
| Gobuster | Apache License 2.0 | not mandatory |
| httprobe | Tom Hudson - | mandatory |
| nmap | GNU General Public License v2.0 | not mandatory |
Dependencies
$ pip install -r requirements.txt# Linux
=======
apt-get install jq nmap phantomjs
# Mac
brew cask install phantomjs
brew install jq nmapIf you have a Go environment ready to go, it's as easy as:
export GOPATH=$HOME/go
export PATH=$PATH:$GOROOT/bin:$GOPATH/bin
go get -u github.com/tomnomnom/httprobe
go get -u github.com/OJ/gobusterDownload Sudomy From Github
# Clone this repository
git clone --recursive https://github.com/screetsec/Sudomy.git
# Go into the repository
sudomy --helpRunning in a Docker Container
# Pull an image from DockerHub
docker pull screetsec/sudomy:v1.1.0
# Run an image, you can run the image on custom directory but you must copy/download config sudomy.api on current directory
docker run -v "${PWD}/output:/usr/lib/sudomy/output" -v "${PWD}/sudomy.api:/usr/lib/sudomy/sudomy.api" -it --rm screetsec/sudomy:v1.1.0 [argument]Post Installation
API Key is needed before querying on third-party sites, such as
Shodan, Censys, SecurityTrails, Virustotal, and BinaryEdge.- The API key setting can be done in sudomy.api file.
# Shodan
# URL : http://developer.shodan.io
# Example :
# - SHODAN_API="VGhpc1M0bXBsZWwKVGhmcGxlbAo"
SHODAN_API=""
# Censys
# URL : https://censys.io/register
CENSYS_API=""
CENSYS_SECRET=""
# Virustotal
# URL : https://www.virustotal.com/gui/
VIRUSTOTAL=""
# Binaryedge
# URL : https://app.binaryedge.io/login
BINARYEDGE=""
# SecurityTrails
# URL : https://securitytrails.com/
SECURITY_TRAILS=""Usage
___ _ _ _
/ __|_ _ __| (_)(_)_ __ _ _
\__ \ || / _ / __ \ ' \ || |
|___/\_,_\__,_\____/_|_|_\_, |
|__/ v{1.1.0#dev} by @screetsec
Sudomy - Fast Subdmain Enumeration and Analyzer
http://github.com/screetsec/sudomy
Usage: sudomy.sh [-h [--help]] [-s[--source]][-d[--domain=]]
Example: sudomy.sh -d example.com
sudomy.sh -s Shodan,VirusTotal -d example.com
sudomy.sh -pS -rS -sC -nT -sS -d example.com
Optional Arguments:
-a, --all Running all Enumeration, no nmap & gobuster
-b, --bruteforce Bruteforce Subdomain Using Gobuster (Wordlist: ALL Top SecList DNS)
-d, --domain domain of the website to scan
-h, --help show this help message
-o, --html Make report output into HTML
-s, --source Use source for Enumerate Subdomain
-tO, --takeover Subdomain TakeOver Vulnerabilty Scanner
-pS, --ping-sweep Check live host using methode Ping Sweep
-rS, --resolver Convert domain lists to resolved IP lists without duplicates
-sC, --status-code Get status codes, response from domain list
-nT, --nmap-top Port scanning with top-ports using nmap from domain list
-sS, --screenshot Screenshots a list of website
-nP, --no-passive Do not perform passive subdomain enumeration
--no-probe Do not perform httprobe
To use all 16 Sources and Probe for working http or https servers:
___ _ _ _
/ __|_ _ __| (_)(_)_ __ _ _
\__ \ || / _ / __ \ ' \ || |
|___/\_,_\__,_\____/_|_|_\_, |
|__/ v{1.1.0#dev} by @screetsec
Sudomy - Fast Subdmain Enumeration and Analyzer
http://github.com/screetsec/sudomy
Usage: sudomy.sh [-h [--help]] [-s[--source]][-d[--domain=]]
Example: sudomy.sh -d example.com
sudomy.sh -s Shodan,VirusTotal -d example.com
sudomy.sh -pS -rS -sC -nT -sS -d example.com
Optional Arguments:
-a, --all Running all Enumeration, no nmap & gobuster
-b, --bruteforce Bruteforce Subdomain Using Gobuster (Wordlist: ALL Top SecList DNS)
-d, --domain domain of the website to scan
-h, --help show this help message
-o, --html Make report output into HTML
-s, --source Use source for Enumerate Subdomain
-tO, --takeover Subdomain TakeOver Vulnerabilty Sca nner
-pS, --ping-sweep Check live host using methode Ping Sweep
-rS, --resolver Convert domain lists to resolved IP lists without duplicates
-sC, --status-code Get status codes, response from domain list
-nT, --nmap-top Port scanning with top-ports using nmap from domain list
-sS, --screenshot Screenshots a list of website
-nP, --no-passive Do not perform passive subdomain enumeration
--no-probe Do not perform httprobe
To use one of more source:
$ sudomy -d hackerone.comTo use one or more plugins:
$ sudomy -s shodan,dnsdumpster,webarchive -d hackerone.com$ sudomy -pS -sC -sS -d hackerone.comTo create report in HTML Format
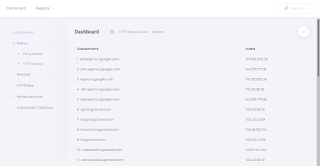
$ sudomy --all -d hackerone.comHTML Report Sample:
| Dashboard | Reports |
|---|---|
Tools Overview
- Youtube Videos : Click here
Translations
- Tom Hudson - Tomonomnom
- OJ Reeves - Gobuster
- Thomas D Maaaaz - Webscreenshot
- Daniel Miessler - SecList
- EdOverflow - can-i-take-over-xyz
- jerukitumanis - Docker Maintainer
- NgeSEC Community
- Gauli(dot)Net
- Bugcrowd & Hackerone
Regards
Kang Asu