Get Rid of lpcloudbox329.com Pop-ups and Fix Chaos
![Get Rid of lpcloudbox329.com Pop-ups and Fix Chaos]() Reviewed by 0x000216
on
Saturday, May 24, 2014
Rating: 5
Reviewed by 0x000216
on
Saturday, May 24, 2014
Rating: 5
Remove/ Get Rid of Horoscope.gateable.com Pop-ups Completely
![Remove/ Get Rid of Horoscope.gateable.com Pop-ups Completely]() Reviewed by 0x000216
on
Saturday, May 24, 2014
Rating: 5
Reviewed by 0x000216
on
Saturday, May 24, 2014
Rating: 5
Kali Linux Live USB Install
Booting and installing Kali from a USB stick is our favorite and fastest method of getting up and running. In order to do this, we first need to create the Kali ISO image on a USB drive. If you would like to add persistence to your Kali Linux USB stick, please read the full document before proceeding to create your image.
Preparing for the USB copy
- Download Kali linux.
- If running Windows, download Win32 Disk Imager.
- No special software is needed for a *nix OS.
- A USB Key (at least 2GB capacity for mini, 4GB for regular).
Kali Linux Live USB Install Procedure
Imaging Kali on a Windows Machine
- Plug your USB stick into your Windows USB port and launch the Win32 Disk Imager software
- Choose the Kali Linux ISO file to be imaged and verify that the USB drive to be overwritten is the correct one.
- Once the imaging is complete, safely eject the USB drive from the Windows machine. You can now use the USB device to boot into Kali Linux.
Imaging Kali on a Linux Machine
Creating a bootable Kali Linux USB key in a Linux environment is easy. Once you’ve downloaded your Kali ISO file, you can use dd to copy it over to your USB stick as follows (make sure your root first):
WARNING. Although the process of imaging Kali on a USB stick is very easy, you can just as easily destroy arbitrary partitions with dd if you do not understand what you are doing. Consider yourself warned.
- Plug in your USB device to your Linux computer’s USB port.
- Verify the device path of your USB storage with dmesg.
- Proceed to (carefully!) image the Kali ISO file on the USB device:
dd if=kali.iso of=/dev/sdb bs=512k
That’s it, really! You can now boot into a Kali Live / Installer environment using the USB device.
Adding Persistence to Your Kali Live USB
Adding persistence (the ability to save files and changes across live boots) to your Kali Linux image can be very useful in certain situations. To make your Kali Linux USB stick persistent, follow these steps as the root user. In this example, we assume our USB drive is /dev/sdb. If you want to add persistence, you’ll need a larger USB device than we listed in our prerequisites above.
- Image the Kali Linux ISO to your USB stick as explained above, using the “Linux Method” and dd.
- Create and format an additional partition on the USB stick. In our example, we usegparted by invoking: gparted /dev/sdb
- Your current partitioning scheme should look similar to this:
- Proceed to format a new partition of your desired size to be used for persistence. In our example, we used all the remaining space available. Make sure the volume label of the newly created partition is persistence, and format it using the ext4 filesystem.
- Once the process is complete, mount your persistence USB partition using the following commands (as the root user):mkdir /mnt/usb
mount /dev/sdb2 /mnt/usb
echo "/ union" >> /mnt/usb/persistence.conf
umount /mnt/usb - Plug the USB stick into the computer you want to boot up. Make sure your BIOS is set to boot from your USB device. When the Kali Linux boot screen is displayed, select “Live boot” from the menu (don’t press enter), and press the tab button. This will allow you to edit the boot parameters. Add the word “persistence” to the end of the boot parameter line each time you want to mount your persistent storage.
Kali Linux Live USB Install
![Kali Linux Live USB Install]() Reviewed by 0x000216
on
Saturday, May 24, 2014
Rating: 5
Reviewed by 0x000216
on
Saturday, May 24, 2014
Rating: 5
Kali Linux vs BackBox
We blog a lot on Linux pentesting distros (here’s our top-ten list) and it was really a question of time before we wrote this particular post comparing these two popular Linux distros.
Kali Linux vs BackBox is essentially an exercise, in our opinion, of comparing Ubuntu (which BackBox is based on) to Debian (which Kali Linux is based upon). We need to set the record straight now because we are massive BackBox fans. We run several machines (hard booted) in the office and are very happy with it. Our personal story is that we used to run BackTrack back in the day but we became very impatient with a few nagging issues that we always had, mostly with drivers not working and tools not being updated correctly. We switched to BackBox just prior to the Kali Linux launch and never really left BackBox. So with that being said, yes, we are biased but, we also know of course that Kali has a massive following and popularity base so clearly the guys at Offensive Security (the people behind the distro) have done a great job.
So why this post?
In May 14 of this year we posted a poll titled: “Vote for your favorite Linux Penetration Testing Distribution” and, several months later, and 317 votes later (as of July 28th 2013) we are really happy to see that BackBox is not that far behind Kali – which is really encouraging considering the massive fan base that Kali Linux enjoys.
In May 14 of this year we posted a poll titled: “Vote for your favorite Linux Penetration Testing Distribution” and, several months later, and 317 votes later (as of July 28th 2013) we are really happy to see that BackBox is not that far behind Kali – which is really encouraging considering the massive fan base that Kali Linux enjoys.
Here are the results of the poll so far, (by the way you can still vote if you want, voting will remain open – forever!)
84% voted for Kali Linux Pentesting Hacking Distro
84% Prefer Kali Linux
77% voted for BackBox Pentesting Hacking Distro
77% Prefer BackBox
7% voted for Bugtraq
60% Complete (warning)
- Kali Linux
- BackBox
- Knoppix STD
- Pentoo
- DEFT
- CAINE
- Samurai Web Testing Framework
- Matriux Krypton
- WEAKERTH4N
- Bugtraq
- NodeZero
- Fedora Security Spin
So why one over the other?
The choice really shouldn’t be that difficult because essentially they all do the same thing. In fact we’d really like to hear your comments below because we bet you have the same reasons as us, i.e. you just fell into a distro and that was that. Most of our Hacker Hotshot speakers tend to favor Kali, it is a question that we often ask them because a lot of their research is conducted from Linux Operating Systems and Distros.
The choice really shouldn’t be that difficult because essentially they all do the same thing. In fact we’d really like to hear your comments below because we bet you have the same reasons as us, i.e. you just fell into a distro and that was that. Most of our Hacker Hotshot speakers tend to favor Kali, it is a question that we often ask them because a lot of their research is conducted from Linux Operating Systems and Distros.
Drivers, and the support that the developers give to ensuring drivers work, is clearly a motivating factor to why you might chose one pentesting distro over another, and again, this is what made us switch from BackTrack to BackBox. However, in our opinion – here is the biggest reason why someone would prefer one over the other, and that reason is support. The support that Offensive Security can afford to give to Kali is huge. Their forum is huge and as a result there is a lot of answered questions to ‘common’ problems. So, if you are new to the scene and are having trouble with a particular security tool, install, or whatever – then fear not, someone over at Kali will assist.
In our opinion the fine folks over at BackBox headed by community leader ZEROF are a more friendly bunch and more n00b friendly than any other pentesting forum.
Also, it’s worth mentioning here that BackBox is a very Italian affair. Many of the community members are Italian and Founder Raffaele Forte along with Repository Maintainer Alessio Pascolini, we think, judging by their names, are also Italian. Just a side note, but we have noticed other hacking and forensics/ pentesting/ security distros hailing from Italy – not sure why that is but anyway here are another two from Italy: CAINE and we think also DEFT8?
Anyway – the main point we are making here is that of support. No support makes life difficult. We prefer the slightly more user-friendly and helpful support from BackBox, but if you like mass appeal then Kali is your new friend.
Which has the most tools?
Well, rather than re-invent the wheel – here is an exhaustive list of security tools that are contained within Kali Linux and trust me on this, there are enough here for you to be getting on with. The latest version of BackBox 3.05 has new and updated hacking tools (that include automater, inundator, ettercap, wireshark, se-toolkit, metasploit, sqlmap, beef, weevely, thc-ipv6, truecrack, hashcat, and more).
Well, rather than re-invent the wheel – here is an exhaustive list of security tools that are contained within Kali Linux and trust me on this, there are enough here for you to be getting on with. The latest version of BackBox 3.05 has new and updated hacking tools (that include automater, inundator, ettercap, wireshark, se-toolkit, metasploit, sqlmap, beef, weevely, thc-ipv6, truecrack, hashcat, and more).
We do not know if there are any ‘missing tools’ in either distro and to do a comparison would take rather a long time, but please let us know in the comments below if you have ever come across a pentesting tool that you think ought to be in either one of the distros.
Sidenote, if WireShark is your thing then come and join us July 31st at 1200 EST for a: How to Hack VoIP (and defend your netowrk!) using WireShark. Also – on the subject of hacking tools you might like this post, “On My Command. Unleash Hell! The Black Hat Arsenal 2013!”.
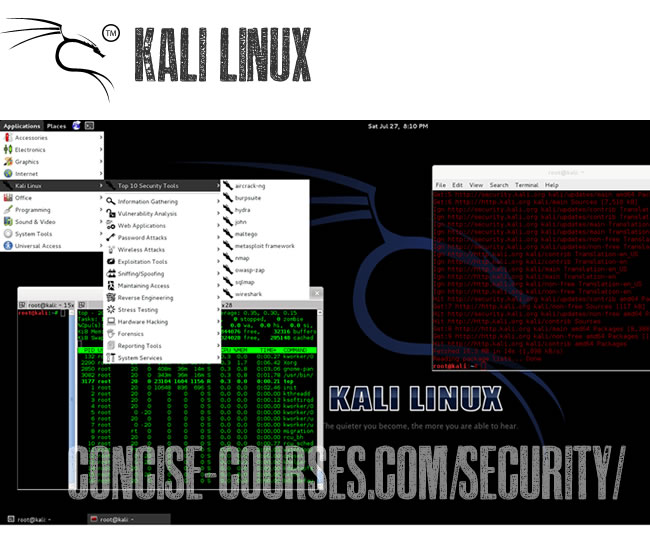
Quick Summary: Kali Linux
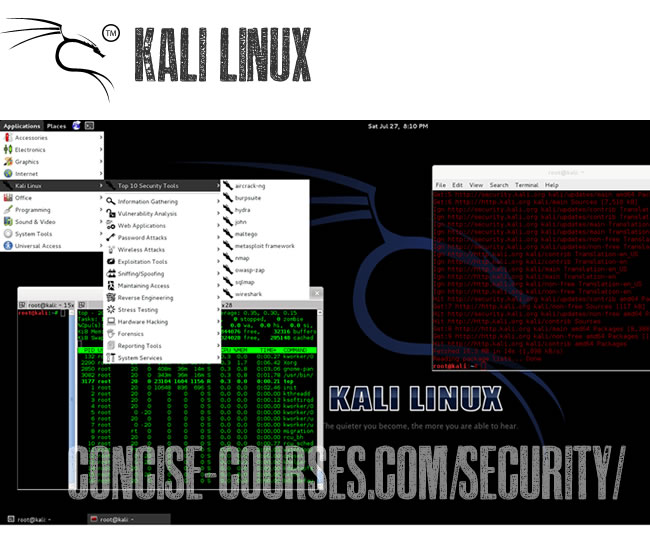
Quick Summary: Kali Linux
- OS Type: Linux
- Based on: Debian
- Version 1.0
- Origin: USA
- Architecture: i386, x86_64, ARM
- Desktop: Gnome, KDE, XFCE

Quick Summary: BackBox
- OS Type: Linux
- Based on: Debian, Ubuntu
- Version 3.05
- Origin: Italy
- Architecture: i386, x86_64
- Desktop: XFCE
In summary
We are totally biased to BackBox and for that we reason we need your input! Please leave a comment below and let us know your favorite Linux pentesting distro! Our voting will remain open throughout 2013 giving you a chance to cast your all important ballot! Vote on your favorite distro here!
We are totally biased to BackBox and for that we reason we need your input! Please leave a comment below and let us know your favorite Linux pentesting distro! Our voting will remain open throughout 2013 giving you a chance to cast your all important ballot! Vote on your favorite distro here!
Our decision to switch to Backbox came on the back of a buggy BackTrack 3 and 4, and the fact that BackBox with XFCE was lightning fast and, frankly, we have never had an issue with the distro.
What’s yours?
Kali Linux vs BackBox
 Reviewed by 0x000216
on
Saturday, May 24, 2014
Rating: 5
Reviewed by 0x000216
on
Saturday, May 24, 2014
Rating: 5
 Reviewed by 0x000216
on
Saturday, May 24, 2014
Rating: 5
Reviewed by 0x000216
on
Saturday, May 24, 2014
Rating: 5
How To Update Kali Linux
Kali Linux’s Penetration testing system requires constant updating to keep the tools in functional order. This short tutorial will show you the command to update the tools and system.
Step One:
Start Kali Linux and open a terminal.

Step Two:
Type apt-get update && apt-get upgrade (without quotes) in the terminal and hit Enter.

Kali will now check it’s webservers for updates. If there are any, it will ask you if you want to install them, hit Enter for yes. It’s hard to remember that long command at first, so I suggest checking out my post on how to create Permanent Aliases In Kali Linux.
Step One:
Start Kali Linux and open a terminal.

Step Two:
Type apt-get update && apt-get upgrade (without quotes) in the terminal and hit Enter.

Kali will now check it’s webservers for updates. If there are any, it will ask you if you want to install them, hit Enter for yes. It’s hard to remember that long command at first, so I suggest checking out my post on how to create Permanent Aliases In Kali Linux.
Thank you!
How To Update Kali Linux
 Reviewed by 0x000216
on
Saturday, May 24, 2014
Rating: 5
Reviewed by 0x000216
on
Saturday, May 24, 2014
Rating: 5
 Reviewed by 0x000216
on
Saturday, May 24, 2014
Rating: 5
Reviewed by 0x000216
on
Saturday, May 24, 2014
Rating: 5
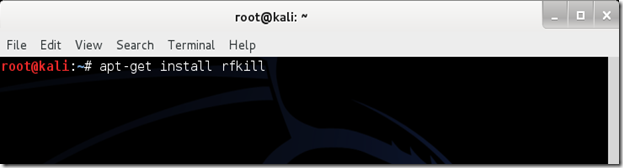
How To Install rfkill In Kali Linux
You may be trying to do some advanced networking in Kali. The tutorial you are following says: “type rfkill block all.” You try, and are presented with: an ERROR MESSAGE!? Don’t panic, there is an easy way to install rfkill in Kali Linux.
Step One:
Start Kali Linux and open a terminal.
Step Two:
Type: apt-get install rfkill
Step Three:
Kali Linux will now check its databases and ask if you want to install rfkill. Type y for yes.
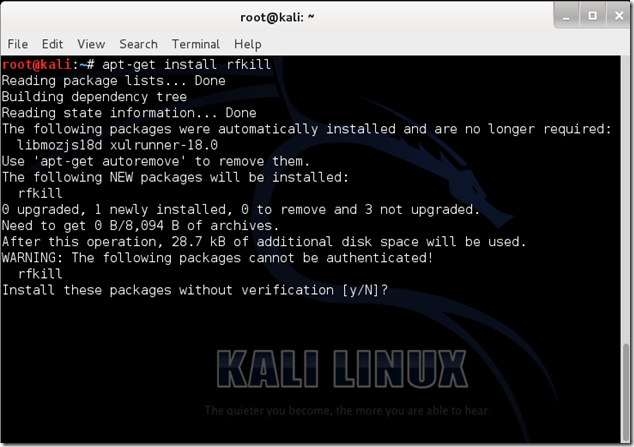
Kali Linux will now finish the process of installing rfkill. Never stop an installation once it has started! This might ruin Kali.
Finished, thank you for viewing!
We’d appreciate your feedback!
If you have time, please comment or contact me using the form below
How To Install rfkill In Kali Linux
 Reviewed by 0x000216
on
Saturday, May 24, 2014
Rating: 5
Reviewed by 0x000216
on
Saturday, May 24, 2014
Rating: 5
 Reviewed by 0x000216
on
Saturday, May 24, 2014
Rating: 5
Reviewed by 0x000216
on
Saturday, May 24, 2014
Rating: 5
How To Make A Permanent Alias In Kali Linux
Since the Linux operating system is based almost entirely on terminal commands, it is imperative that you create some basic aliases to make your life a bit easier. One way of doing this is to just issue the command, “alias=command.” The problem with this method is that it only keeps the alias until the system is logged off, then you have to enter it all over again.
The solution? Enter the alias in the .bashrc file. This simple tutorial will explain to you how to do this.
The solution? Enter the alias in the .bashrc file. This simple tutorial will explain to you how to do this.
Step one:
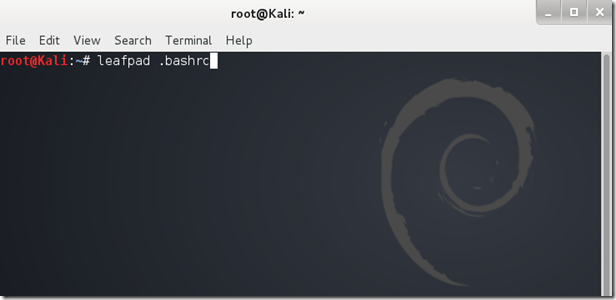
Log into Linux and open a terminal.
Step two:
Hit Enter. A text file (.bashrc) should open in the leafpad text editor.
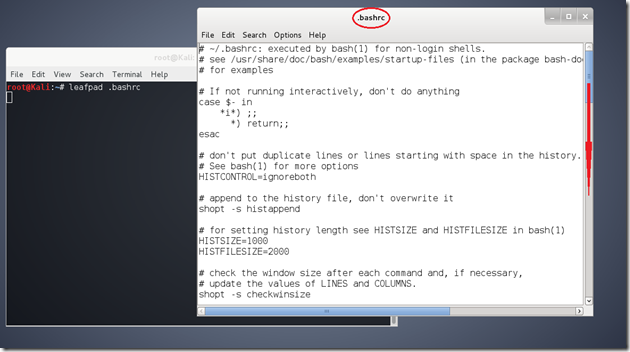
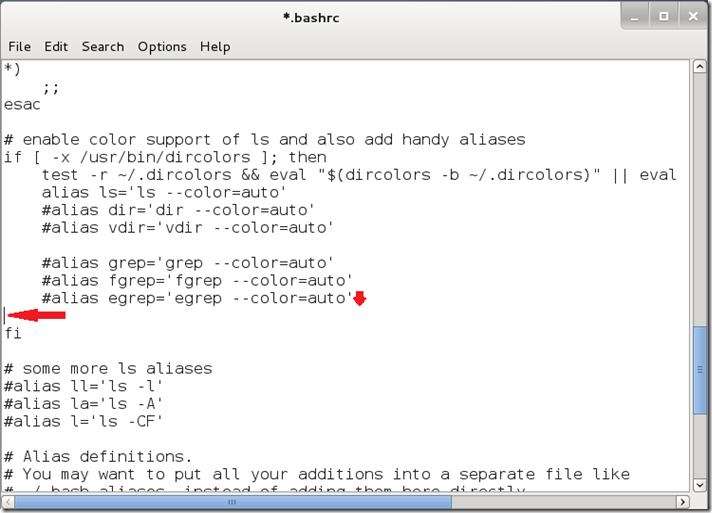
Scroll down until you reach a line filled with #alias examples.
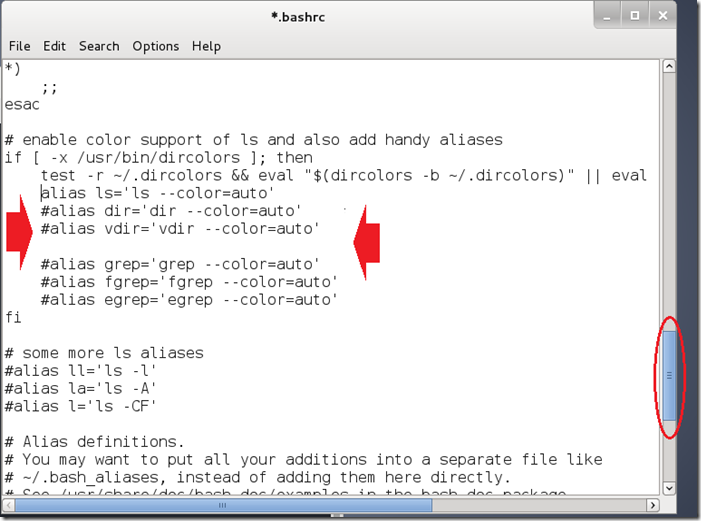
Step four:
Scroll down until you reach a line filled with #alias examples.
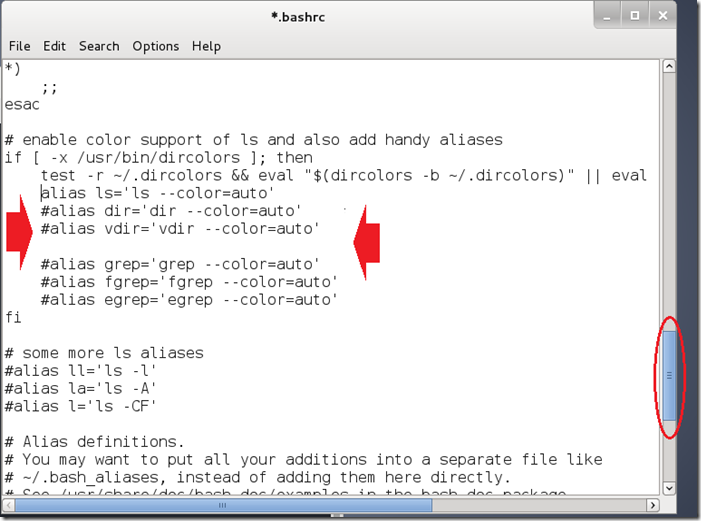
Step four:
Place your select cursor at the end of the last #alias example and hit enter, making a new line. See photo below.
Step five:
Type the alias in the specified above location using the following format:
alias [shortcut]='[command]'Replace [shortcut] with the alias you want, and replace [command] with the command that the alias stands for.
Example: alias updatesys='apt-get update && apt-get upgrade'
The above example is a alias that I use so I can easily update Kali without having to type in “apt-get update && apt-get upgrade” every time.
Picture example:

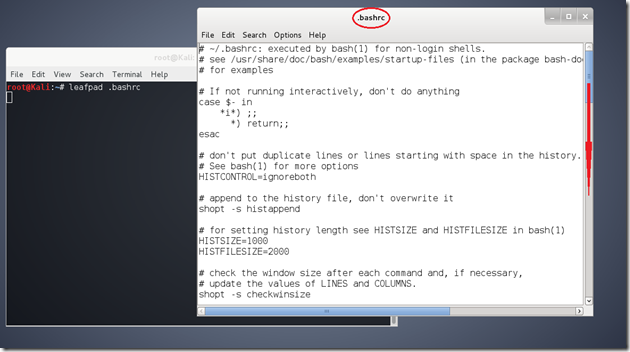
Final step:
You’re almost there! Now that you’re done typing the alias in, you need to save the .bashrc file. Do this quickly by hitting Ctrl+S or click “File > Save.”
Tip:
To insure that the file has been completely saved, make sure that the asterisk next to the file name is gone:

Now close the .bashrc file and the terminal behind it. Open a new terminal and try out your alias. If all went according to plan, the alias will be permanent, and can only be removed if you remove it from the .bashrc file in the same way you created it.
Congrats! You’re done!
Repeat these steps to create as many permanent aliases as you please!
If you have any trouble, just comment or contact me using the form below.
How To Make A Permanent Alias In Kali Linux
 Reviewed by 0x000216
on
Saturday, May 24, 2014
Rating: 5
Reviewed by 0x000216
on
Saturday, May 24, 2014
Rating: 5
 Reviewed by 0x000216
on
Saturday, May 24, 2014
Rating: 5
Reviewed by 0x000216
on
Saturday, May 24, 2014
Rating: 5
Perform A Man In The Middle Attack With Kali Linux & Ettercap
It’s one of the simplest but also most essential steps to “Conquering” a network. Once a hacker has performed a “Man In The Middle” attack (MITM) on a local network, he is able to perform a number of other “Side-kick” attacks. This includes, cutting a victim’s internet connection; intercepting Emails, logins, and chat messages; and many others.
And only one tools is needed for this attack:
- An install or Live boot of Kali Linux, a well-known OS containing a collection of hundreds of penetration testing tools.
If you have that, then proceed to the tutorial below, and we’ll demonstrate how to perform this powerful attack.
Important Notice: This tutorial is intended to be used for penetration testing, i.e. the act of hacking to become more secure. It is not at all meant for malicious purposes. Performing any type of fraudulent activity on someone else’s network without permission is considered a crime in most countries. Lewis’s Computer How-to’s is using their own test network in this demonstration. By reading and/or using the information below, you are agreeing that:
We not responsible for misuse of this information in any illegal/criminal way.
Step One:
Start Kali Linux and login to the root user.
Step Two:
Open a Terminal and type: leafpad /etc/ettercap/etter.conf
Step Three:
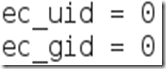
Look through the text file that just opened. On one of the first lines, under the [privs] section, look for the words highlighted below:
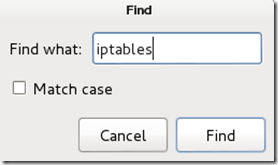
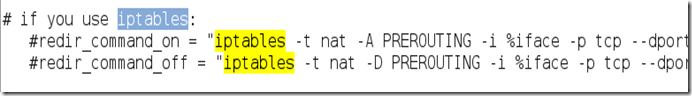
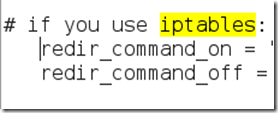
You need to change these lines to this:By removing the number 65534 and replacing it with 0 (zero). You can leave the “# nobody is default” line.Step Four:This next one will be tricky to locate, so we’re going to use the “Find” option. Click on Searchin the toolbar at the top of leafpad and click Find.Type the word iptables in the box that appears and click the Find button or press Enter.It should skip to a line that looks like this:We need to “uncomment” the two bottom lines. To do this, remove the two “#” symbols before each “redir_command,” so that the two lines look like this:
Now close leafpad and click Yes when it asks you to save changes.
Step Five:
Now start Ettercap-gtk, open a Terminal and type ettercap –G
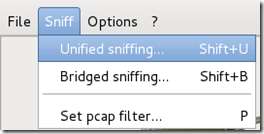
Wait until Ettercap opens. When it does, click Sniff in the toolbar and select Unified Sniffing… from the menu.
Step Six:
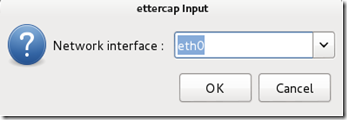
Select the interface that’s connected to the network.
If your using a wired (ethernet) connection, then the interface will probably be eth0, but if you’re using wireless, (WLAN), then it will be a different one. To find which one of your interfaces is connected, run ifconfig.
Step Seven:
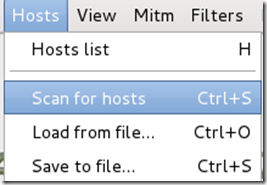
Now Ettercap should load into attack mode. Click on Hosts and select Scan for hosts from the menu.
Step Eight:
Ettercap will briefly scan for hosts on the network. After a moment, you should see the words “hosts added to the host list…” in the command box. This is the green light.
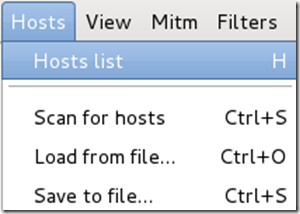
Click on Hosts again, and this time select Hosts list from the menu.
Step Nine:
Click the IP address of the router and click the Add to Target 1 button.
Then select the IP of your test victim’s machine and click Add to Target 2.
Step 10:
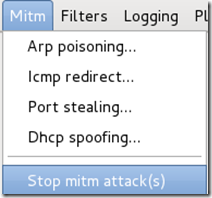
Now click Mitm on the toolbar and select Arp poisoning…
When the question box shows up, check the box next to Sniff remote connections and hitOK.
Step 11:
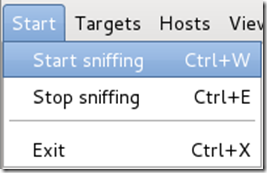
Ettercap will now Arp poison the victim and router. Now if you want to see any of the victim’s personal info, you’ll need to click Start on the toolbar and select Start sniffing.
Ettercap will notify you that unified sniffing was started.
You’ve successfully executed an MITM attack!
You can now use tools such as URLsnarf and SSLstrip to sniff out information about your victim’s internet traffic. Tutorials on how to use these tools will be coming soon.
To stop the MITM attack, click on MITM and select Stop mitm attack(s) from the menu.
Ettercap will then send the ARP correction packet, and the network will return to normal. You can then close Ettercap.
Ways to protect yourself against one of these attacks.
There are a couple of methods:
- ARP detection software
This method is pretty useless. There are very few ARP detection programs out there, and the few that do exist are either free junk or over priced. In addition, to use these programs on a windows machine requires installing special drivers for your wireless cards.
- Static ARP entries
This method works the best for the standard individual. You just type in a simple command and your computer becomes “Unarpable.” This is how it works:
When an attacker performs an ARP MITM attack, his computer sends a ARP packet to the victim’s machine telling it that his mac address is the router’s. The victim’s machine is fooled and starts sending its data to the attacker.
When you enter a static ARP entry, you’re telling your computer that the router’s mac address is permanent and will not be changed. Therefore, your computer ignores any phony ARP packets sent by the attacker.
We will be making a tutorial on how to do this soon. In the meantime, you can use Google to find answers.
We Hope You Enjoyed This TutorialIf you had problems, please contact us using the form below
Perform A Man In The Middle Attack With Kali Linux & Ettercap
 Reviewed by 0x000216
on
Saturday, May 24, 2014
Rating: 5
Reviewed by 0x000216
on
Saturday, May 24, 2014
Rating: 5
 Reviewed by 0x000216
on
Saturday, May 24, 2014
Rating: 5
Reviewed by 0x000216
on
Saturday, May 24, 2014
Rating: 5