The investigation into ToTok
Mass Surveillance, is an (un)Complicated Business
triaging a massively popular iOS application, with a dark side
by: Patrick Wardle / December 20, 2019
 CleanMy Mac X
CleanMy Mac X📝 👾 Want to play along?
I’ve uploaded a decrypted copy of the application and decrypted traffic captures:
Download:
Background
Recently, I was approached by the New York Times (NYT) to assist with the investigation into a massively popular iOS application, ToTok.
Apparently “American officials familiar with a classified intelligence” had determined that ToTok, was actually a spying tool. 😱
“It is used by the government of the United Arab Emirates to try to track every conversation, movement, relationship, appointment, sound and image of those who install it on their phones.” -New York Times
Today, we’ll walk thru a triage of the ToTok iOS application.
The main goal of this blog post is to provide the technical details, about how one may go about triaging an iOS application, using ToTok as a “case-study”
That is say, the aim is simply to discuss our analysis procedure and binary analysis, and note some (interesting) observations.
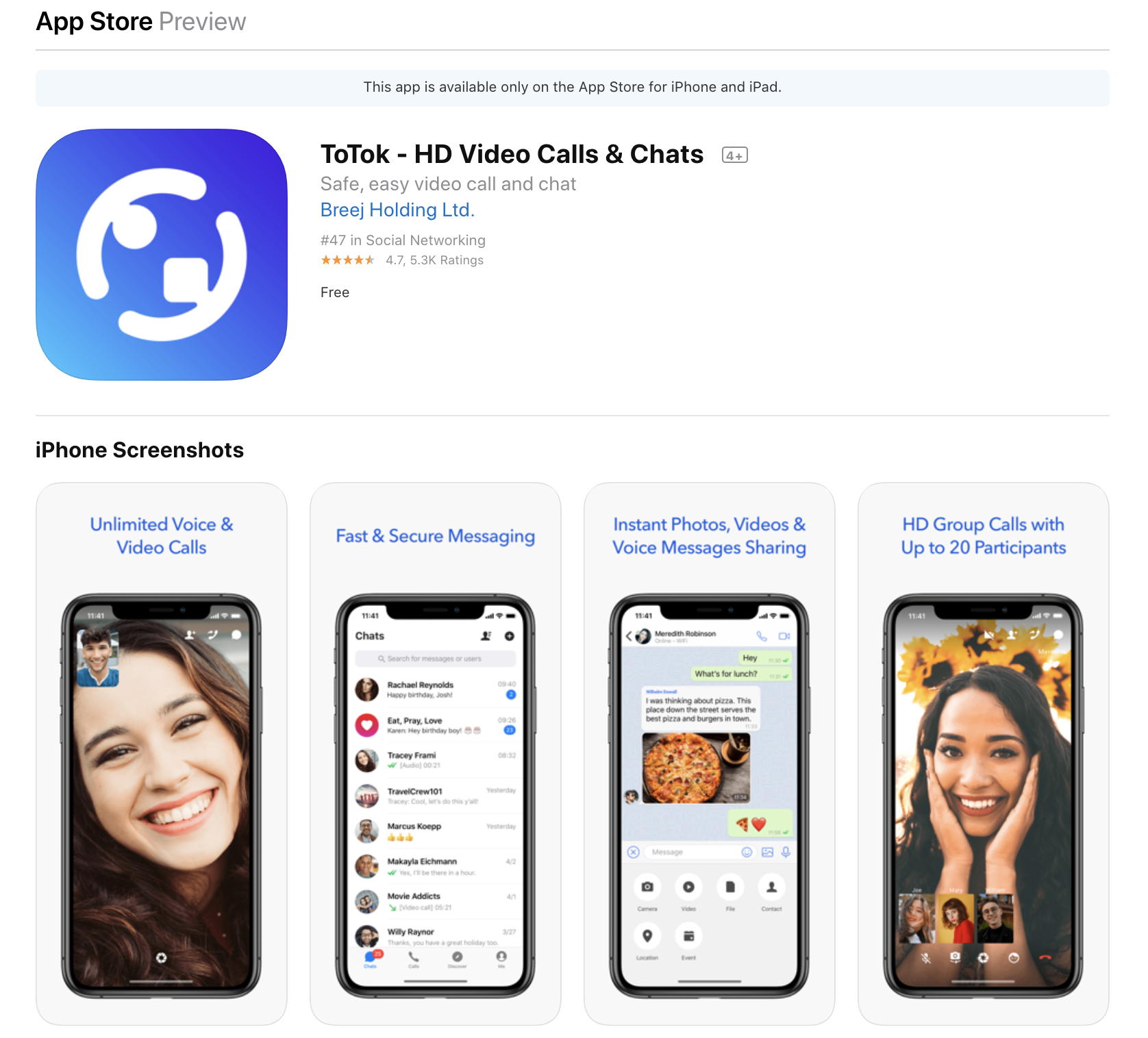
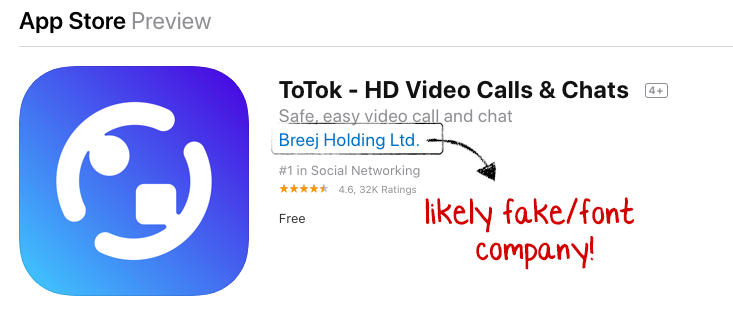
ToTok (by “Breej Holding Ltd.”) is a massively popular application in the United Arab Emirates (UEA). In fact recently it was the #1 “trending” app in Dubai:
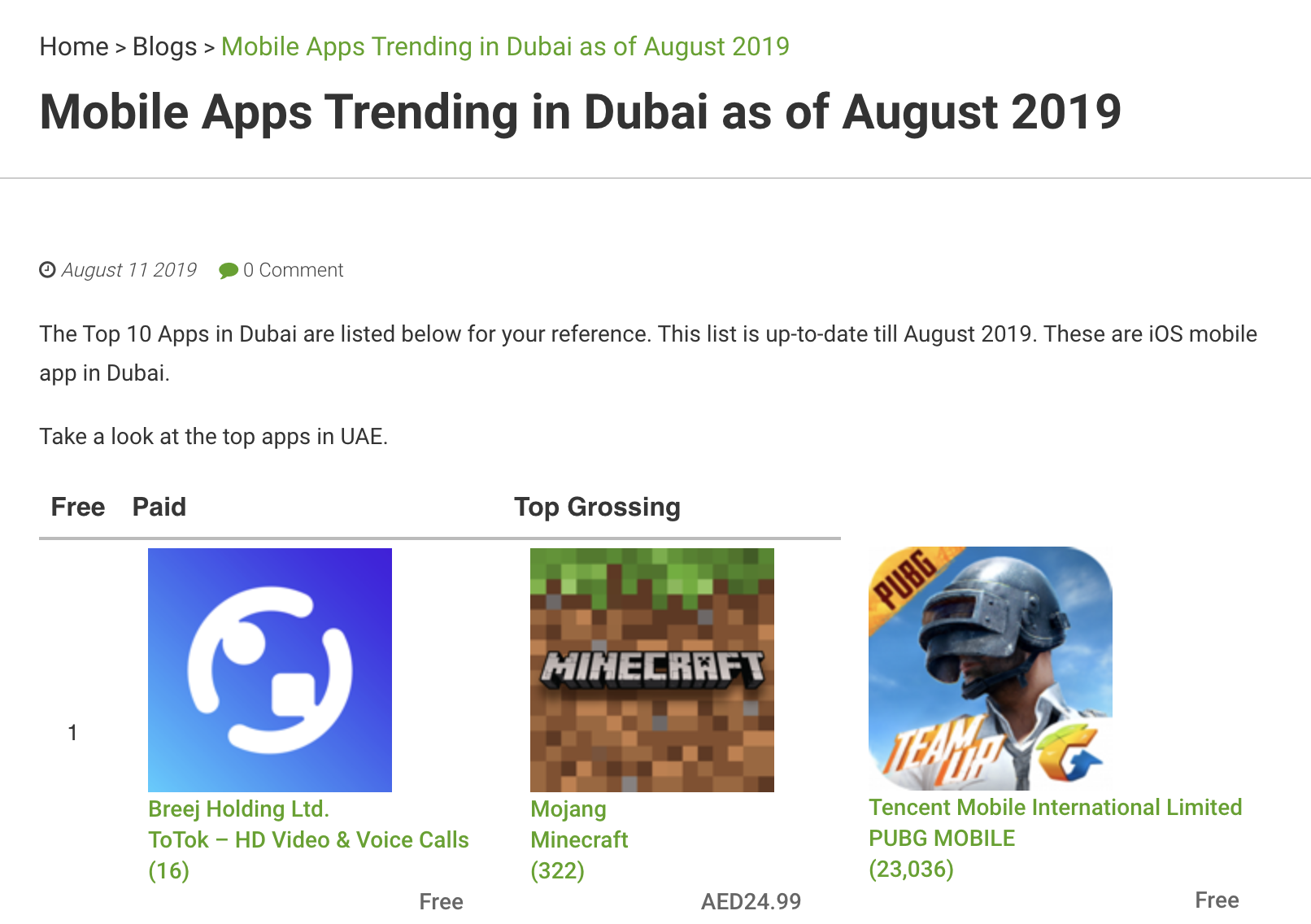
…while on the iOS app store, similarly ranked quite highly: 
It’s reviews (over 32,000!) are largely positive, and mostly laud the fact that this application is not blocked in the UEA (Skype, WhatsApp, etc. are blocked, while using VPNs to access blocked services is illegal).
“Finally a VoIP application which works in UAE. Hopefully it starts this way. The voice and video clarity is simply amazing!! Thanks a lot ToTol and TRA of UAE.” -Mustafa Abdul Ahad
“Really, thank you for this app. I can finally make a call/video call easily with my family since other apps are banned in my current living country. Thankyou” -Jckarhmrv
“I never posted any positive comments or feedback but TOTOK forced me to appreciate your efforts and give love to your unbeatable application. In UAE TOTOK is like water 💧 in desert…” -Saqib Saleem
“…I’m going to give great thanks to all your team that you guys have done great job 😘😘😘 specially for UAE users where all apps are blocked for calling and now this is totally free and still not blocked…” -Pakistan
“Finest app of 2019, really impressive with the way app is designed. Most importantly it works in the UAE and that’s a true blessing” -BeingGaurav
“It’s great to have such an app in a county where Audio & video calls are banned!” -baghya
…it’s almost as if ToTok is too good to be true! 🤔
The app is also recommended on various sites around the Internet, especially as a solution to other apps being blocked in the UAE:
Analysis Setup
Analyzing iOS applications is not the most trivial process, as said applications are distributed (via the iOS App Store) in an encrypted format.
The two main approaches to analyze an iOS application include:
Both are frowned upon by Cupertino, who quickly (when possible) patch all iOS bugs in attempt to thwart jailbreaks or worse, turn to (dubious) legal action.
Unfortunately this leaves security researchers in somewhat of bind, as analysis options are limited.
Apple has promised “developer” devices, to allow independent security researcher both audit iOS proper and analyze iOS applications.
Though these phones have yet to make it into the hands of researches (AFAIK). However if/when they do, they will be hugely welcomed.
Without access a virtualization solution, we’re ‘stuck’ performing our analysis of ToTok on a jailbroken phone. Luckily, thanks to the incredible checkra1n we can jailbreak (and thus analyze iOS applications) even recent versions of iOS!
For details on checkm8/checkra1n see:
Again, mahalo to all the (many) researchers/hackers who made this incredible tool!
Assuming you have access to vulnerable device (iPhone5x - iPhone X), setting up an analysis environment is fairly straightforward, and detailed in “From checkra1n to Frida: iOS App Pentesting Quickstart on iOS 13”:
- Jailbreak with
checkra1n…which installsCydia - Setup
iProxy - Install other tools such as
Frida, etc
Hooray! You’re now able to begin analyzing iOS applications on your (jailbroken) iOS device.
Analyzing ToTok
Now, let’s take a peek at ToTok application.
As this is more of a basic triage (vs. a full-fledged analysis) our goals will be:
First, we install the ToTok application on our jailbroken iOS device:
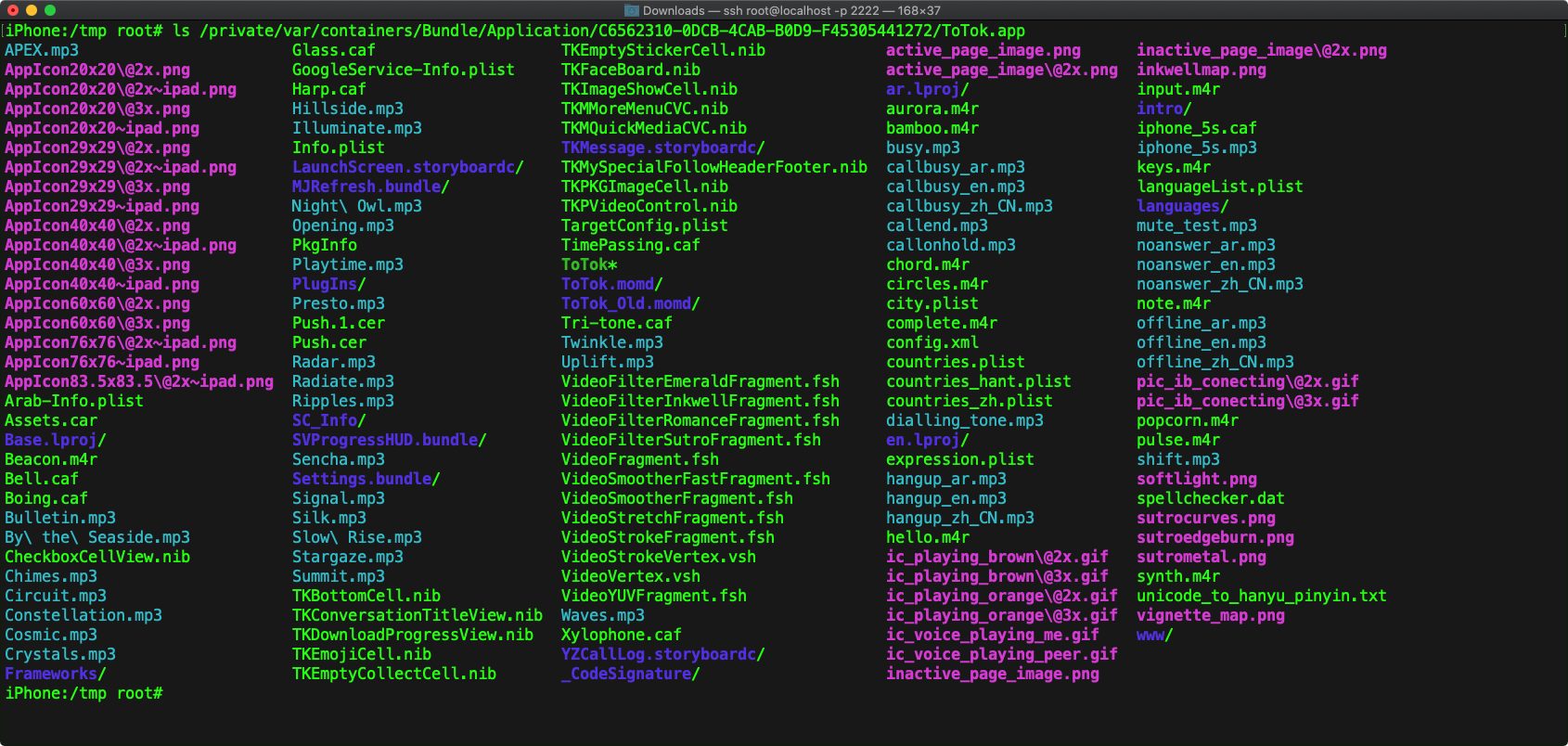
It will end up in the /private/var/containers/Bundle/Application folder (
As noted, the main application binary will be encrypted (via Apple’s FairPlay DRM). We can confirm this by dumping the load commands of the application’s binary (ToTok.app/ToTok) and observing the presence of a LC_ENCRYPTION_INFO_64 command:
otool -Vl ToTok.app/ToTok ... Load command 12 cmd LC_ENCRYPTION_INFO_64 cmdsize 24 cryptoff 253952 cryptsize 4096 cryptid 1 pad 0
We’ll shortly discuss how to fully decrypt the application, but for now there are still lots of unencrypted files to peek at.
Most notably, we can examine the application’s Info.plist file. It’s rather large, but here’s various pieces of it:
$ cat ToTok.app/Info.plistMinimumOSVersion 13.0 CFBundleIdentifier ai.totok.videochat UIBackgroundModes audio fetch remote-notification voip NSAppTransportSecurity NSAllowsArbitraryLoads CFBundleLocalizations en Arabic zh_CN zh_TW FacebookAppID 1454446651523910 NSMicrophoneUsageDescription Allow ToTok to access Microphone to make voice messages and voice/video calls NSCalendarsUsageDescription Allow ToTok to access Calendar to remind you of ToTok Event NSLocationWhenInUseUsageDescription Your location is required for providing local weather informatio NSPhotoLibraryAddUsageDescription Allow ToTok to access Gallery to send/save pictures NSContactsUsageDescription Allow ToTok to read Contacts to find your friends who is using ToTok now NSSiriUsageDescription You can use Siri to call your ToTok contacts directly. NSCameraUsageDescription Allow ToTok to access Camera to take photos and videos
Some observations include:
The presence of the
UIBackgroundModestells iOS that is should (continue) running in the background.
Read more aboutUIBackgroundModesin Apple’s documentation.The
NSAppTransportSecurity/NSAllowsArbitraryLoadskeys tells iOS that the application should be allowed to transmit data via HTTP (normally iOS enforces HTTPS only).
Read more aboutNSAllowsArbitraryLoadsin Apple’s documentation.The
CFBundleLocalizationsarray contains localizations for English, Chinese (zh_CN), Taiwanese (zh_TW), and Arabic.The
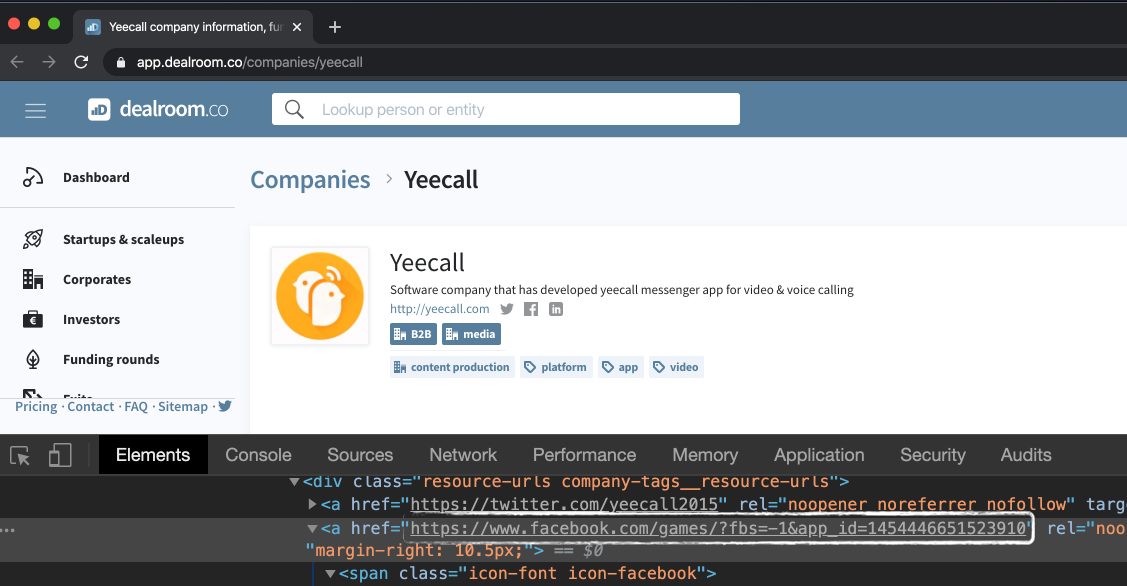
FacebookAppID(1454446651523910) appears to be tied to a company named ‘Yeecall’ (more on this later!)
- The presences of various
*UsageDescriptionkey/value pairs, tells iOS what to display when the app requests permissions.
Here we see theToTokis interested in the: microphone, calendar, location, photos, contacts, siri integration, and camera.
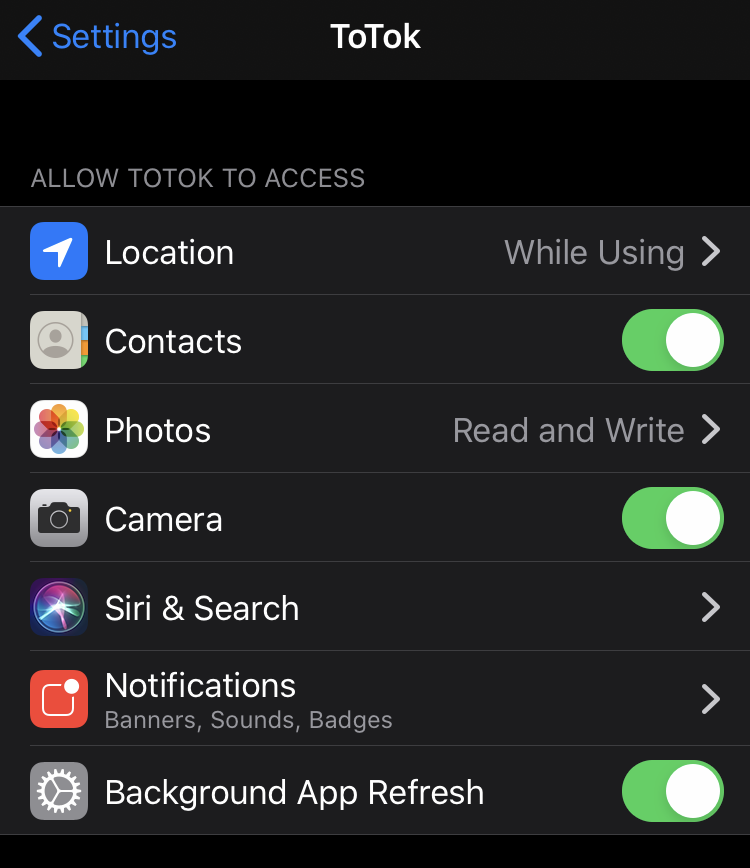
Explicit user approval is required in order for ToTok to be able to access the mic/camera, and user information (photos, location, etc).
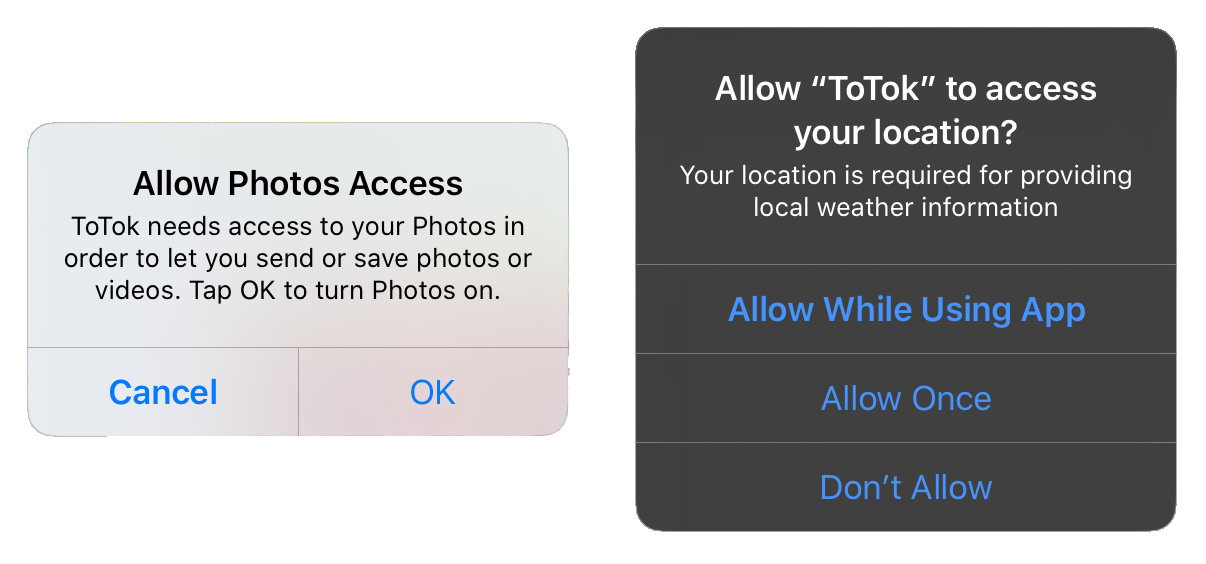
…however such access is required for “legitimate” functionality of the app, and thus, most users will allow.
Before we decrypt the binary to perform static analysis, let’s analyze ToTok’s network traffic.
Network Traffic
Rather unsurprisingly ToToks network communications are all encrypted via SSL. Moreover, the application performs certificate pinning in an attempt to complicate MiTM attacks. However when performing local analysis (on a jailbroken device) neither of these are really obstacles.
First, we setup a remote proxy (say on your MacBook). Then on the iOS device (under the network settings), we specify the address of our proxy to instruct iOS to route all the traffic thru said proxy. I personally use Charles proxy application (though Burp would work as well.
“Charles is an HTTP proxy / HTTP monitor / Reverse Proxy that enables a developer to view all of the HTTP and SSL / HTTPS traffic between their machine and the Internet.” -https://www.charlesproxy.com/
There are several detailed tutorials online the describe how to setup and configure a proxy in order to view (even SSL’d) traffic coming off your iOS device.
In short, we need to install and trust the proxy (Charles’) certificate on the iOS device:
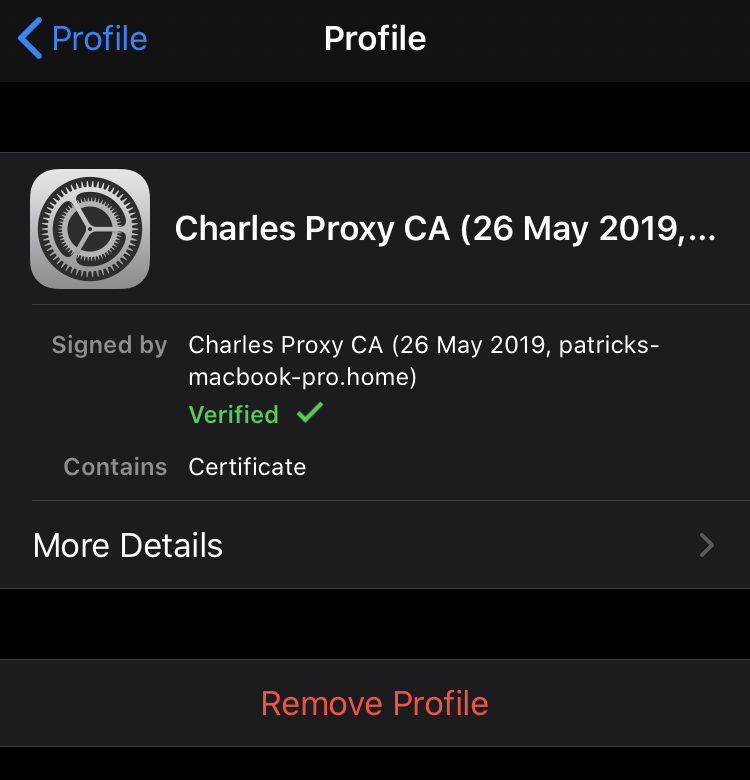
As noted ToTok uses SSL pinning in order to improve the security of its network communications, which means that the application will reject the proxy’s certificate and connections will fail.
Luckily, it’s fairly easy to locally bypass this (so that we can sniff all ToToks traffic) by installing and configuring SSL Kill Switch 2.
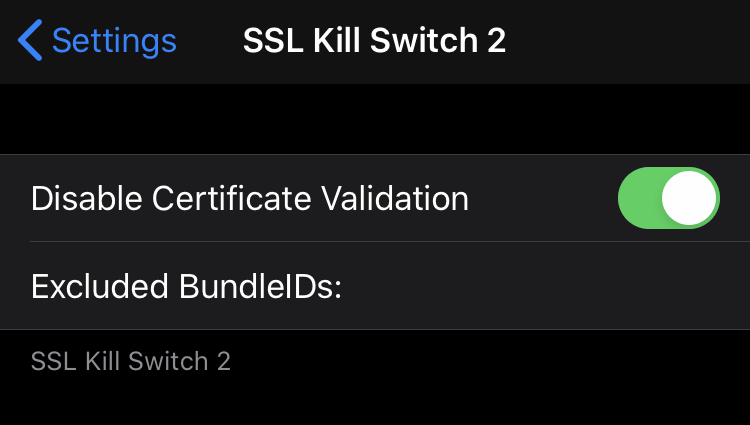
Now we’re all set to sniff ToTok’s encrypted traffic!
Firing up the app, we’re able to observe the (now decrypted) traffic: 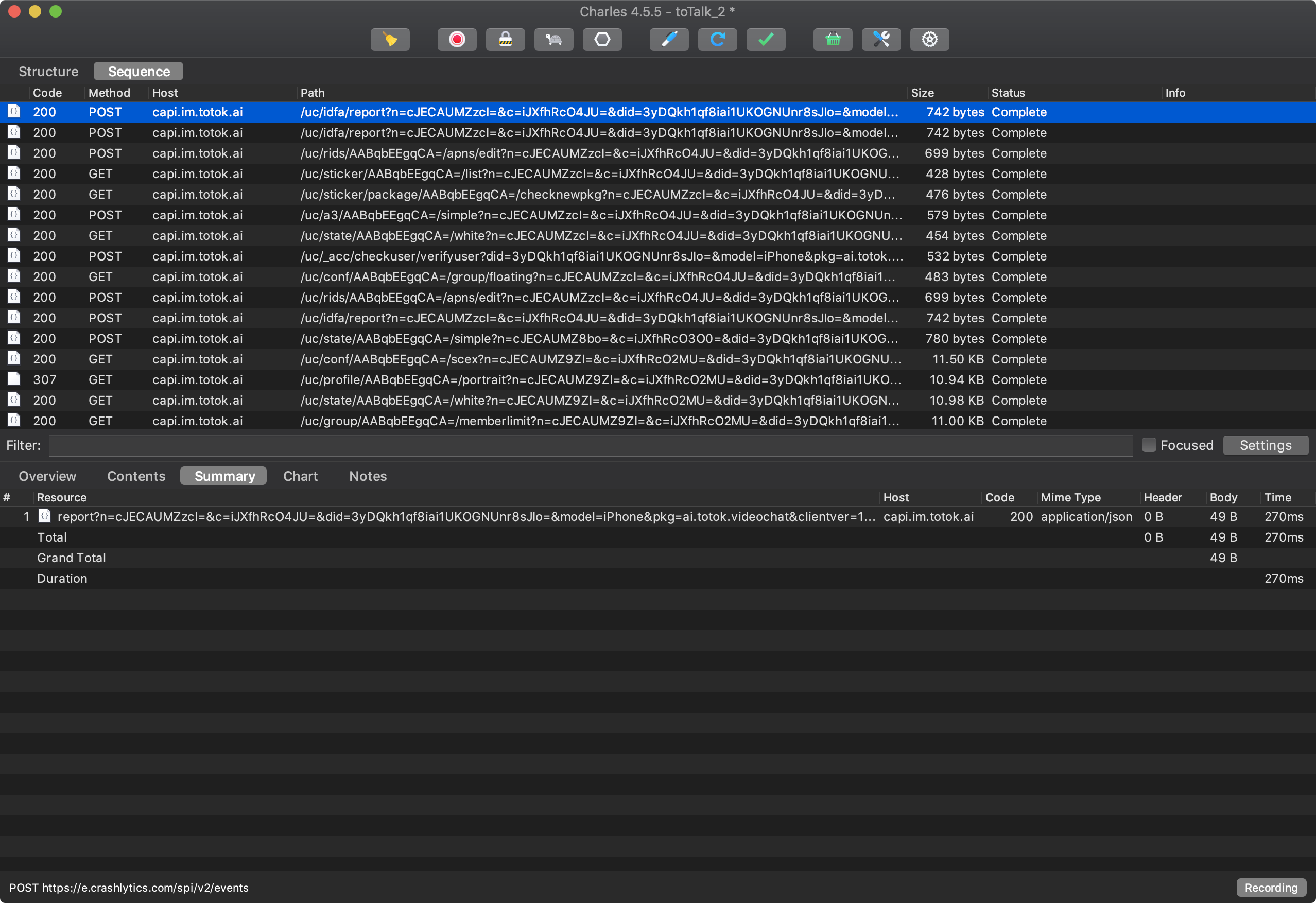
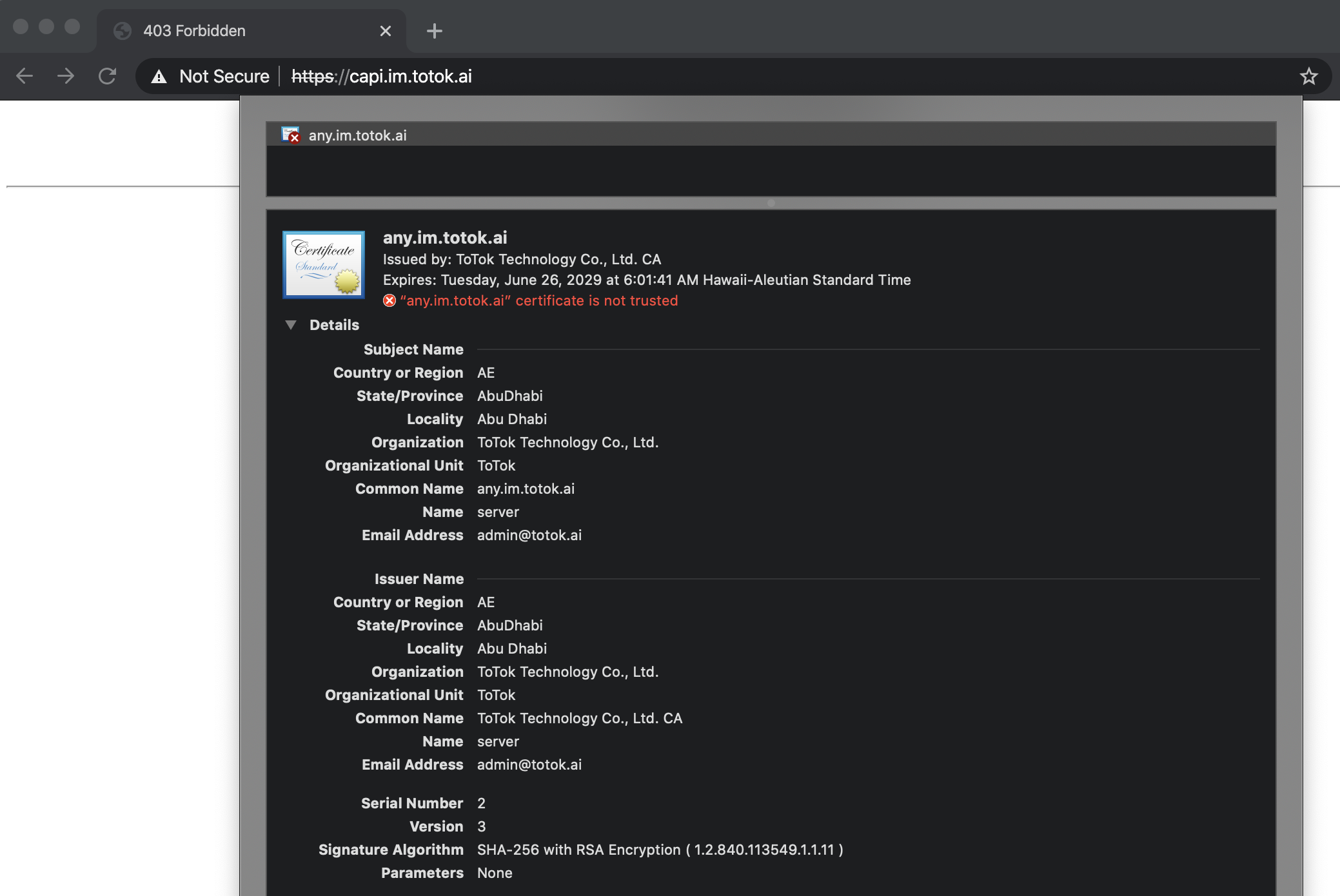
The majority of the application’s traffic routes thru the capi.im.totok.ai server. The server uses a self-signed certificate (SHA-256: C9 27 30 CC D5 FE C0 46 3D E8 5A A6 6D FA AB 2F 3B 92 4E 04 C5 1E 0B 6F A4 31 FE 78 33 48 B5 74), with the issuing country set to AE (United Arab Emirates):
I’ve uploaded two (decrypted) traffic captures (format: Charles Proxy “sessions”).
Download:
The network traffic is fairly standard, for what we’ve expect to see in fully-feature chat application. Here we’ll peruse through some of the requests.
When the app first launches, it makes various GET requests to capi.im.totok.ai.
For example:
https://capi.im.totok.ai/uc/state/AABqbEEgqCA=/white? n=cJECAUMZzcI=&c=iJXfhRcO4JU=&did=3yDQkh1qf8iai1UKOGNUnr8sJIo=&model=iPhone &pkg=ai.totok.videochat&clientver=1.2.9&loc=en-US_US Breaking out the parameters:
- n:
cJECAUMZzcI= - c:
iJXfhRcO4JU= - did:
3yDQkh1qf8iai1UKOGNUnr8sJIo= - model:
iPhone - pkg:
ai.totok.videochat - clientver:
1.2.9 - loc:
en-US_US
The server simply responds with:
{ "response": { "white": false }, "responseHeader": { "status": 200, "version": "1.0" } } Another GET request also to capi.im.totok.ai goes to the /api/idc/find API endpoint, which returns:
{ "response": { "uc": "capi.im.totok.ai", "pfm": "capi.im.totok.ai", "doodle": "in.debug.yeecall.com:8080", "uc_ssl": "capi.im.totok.ai", "pfm_ssl": "capi.im.totok.ai", "doodle_ssl": "capi.im.totok.ai", "idcIdx": 1, "wallet_ssl": "capi.im.totok.ai" }, "responseHeader": { "status": 200, "version": "1.0" } …another reference to yeecall.
Moving on, after verifying the user, the application downloads the user’s profile picture from https://ucdefault-sg.oss-ap-southeast-1.aliyuncs.com/
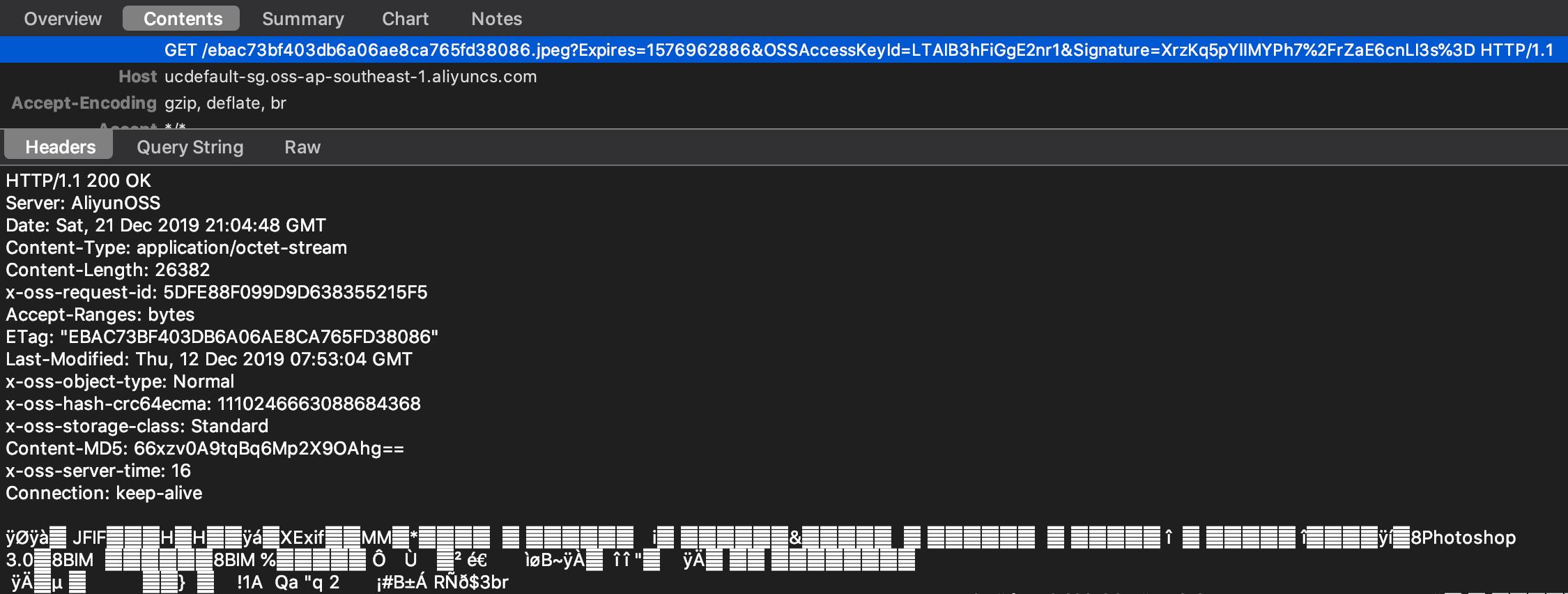
The site, aliyuncs.com, appears to be part of Alibaba’s Cloud.
If the user has authorized ToTok to access their contacts, the app then attempts to upload the entire address book via a POST request:
https://capi.im.totok.ai/log/report/report?n=cJECAUy9BHI=&c=iJXfhRiqKSU=&did=3yDQkh1qf8iai1UKOGNUnr8sJIo=&model=... 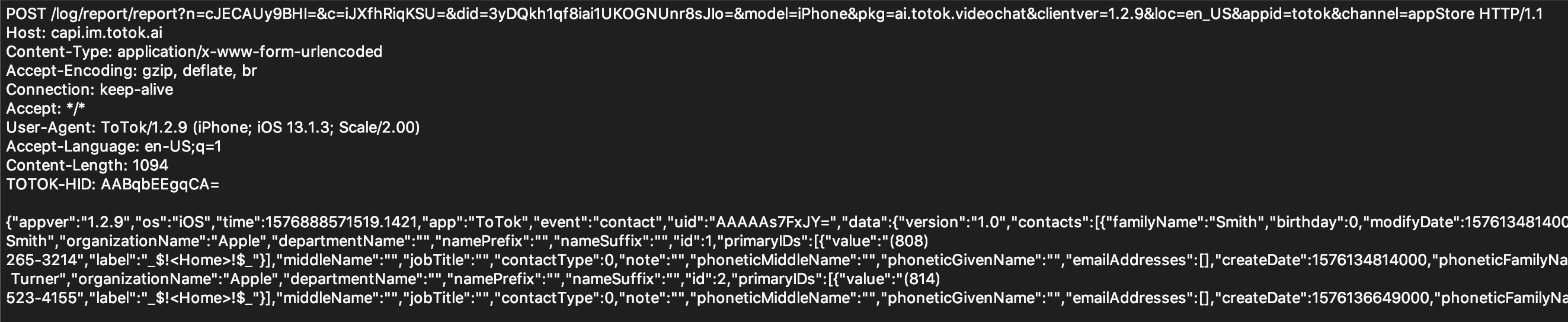
{ "appver": "1.2.9", "os": "iOS", "time": 1576888571519.1421, "app": "ToTok", "event": "contact", "uid": "AAAAAs7FxJY=", "data": { "version": "1.0", "contacts": [{ "familyName": "Smith", "birthday": 0, "modifyDate": 1576134814000, "nickname": "", "displayName": "John Smith", "organizationName": "Apple", "departmentName": "", "namePrefix": "", "nameSuffix": "", "id": 1, "primaryIDs": [{ "value": "(808) 265-3214", "label": "_$!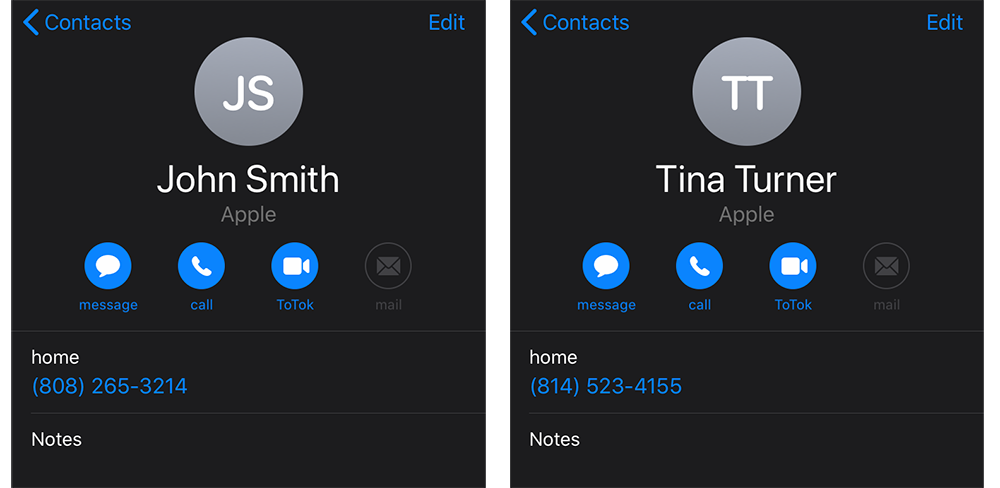
The argument could be made that this is simply (user-approved) “legitimate” functionality of the application, used to connect users with their friends 😬
If media content such as images are transmitted between users, this generates a POST request (with the contents of the file) to https://capi.im.totok.ai/pfm/up/AABqbEEgqCA=/sendtouser to upload the content. The server responds with information about the successful upload:
{ "response": { "download": { "url": "https://capi.im.totok.ai/pfm/download/file?fid=5dfe1lqtkl9555884b0b0001ae7119 ... "size": 81664, "fid": "5dfe1lqtkl9555884b0b0001ae7119", "md5": "a3b89da4ccb998ef9fa66fb11bafcfa1" } }, "responseHeader": { "status": 200, "version": "1.0" } } Prior to upload, it appears that the item (here, an image) is both encrypted and compressed:
00000000 73 d6 6d 3c be 5a d0 43 b6 cb 23 b1 46 b2 c2 b7 |s.m
At this time, it is unknown if the application utilizes end-to-end encryption …or (if so), if said encryption is sufficient.
ToTok’s privacy policy does state:
“Messages: all data is stored heavily encrypted so that local ToTok engineers or physical intruders cannot get access.”
…but this seems to only address “stored data”?
Finally, if the user has authorized ToTok to utilize location services, the app will make a request to meiduoyun.ws.amberweather.com:
https://meiduoyun.ws.amberweather.com/api/v1/weather?appid=12027&lang=en&lat=25.276987&lon=55.296249&pkg=ai.totok.videochat...
Note this request contains the user’s exact geo-coordinates (i.e. lang=en&lat=25.276987&lon=55.296249).
App Decryption
In order to perform static analysis of ToTok, we need to decrypt its application binary.
To decrypt the application binary on our jailbroken analysis device, we use Clutch; a “ high-speed iOS decryption tool.” This utility takes the bundle id of the iOS application to decrypt (e.g. ai.totok.videochat) and outputs a (fully) decrypted .ipa!
root# Clutch -d ai.totok.videochat Clutch[10196:1254709] command: Dump specified bundleID into .ipa file Zipping ToTok.app Dumping (arm64) Patched cryptid (64bit segment) Dumping (arm64) ... Successfully dumped framework ToTokCommonBase! Dumping arm64 Successfully dumped framework PINRemoteImage! Dumping arm64 Dumping arm64 ... Zipping ToTokCommonBase.framework Zipping External.framework Zipping ToTok3rdSDK.framework Zipping ShareExtension.appex DONE: /private/var/mobile/Documents/Dumped/ai.totok.videochat-iOS13.0-(Clutch-(null)).ipa Finished dumping ai.totok.videochat in 9.3 seconds
Another option to dump the encrypted application binary is via Fridump. If run with the -s option, this will also running strings on all the dumped files:
patrick$ python fridump.py -U -s ToTok ______ _ _ | ___| (_) | | | |_ _ __ _ __| |_ _ _ __ ___ _ __ | _| '__| |/ _` | | | | '_ ` _ \| '_ \ | | | | | | (_| | |_| | | | | | | |_) | \_| |_| |_|\__,_|\__,_|_| |_| |_| .__/ | | |_| Current Directory: /Users/patrick/Downloads/fridump-master Output directory is set to: /Users/patrick/Downloads/fridump-master/dump Creating directory... Starting Memory dump... Running strings on all files: Progress: [##################################################] 100.0% Complete Finished!
Either way, we now have a decrypted application bundle and can poke around at the app’s binary code.
As the application (and it’s frameworks) are a massive 25MB+, due to time constraints our analysis is limited.
However, I’ve uploaded the unencrypted ToTok.ipa if you’d like to dig more!
When analyzing a binary, one of the first steps is to extract embedded strings and classes (via Class-dump). This can often shed significant insight into the capabilities of the binary and/or reveal other interesting contact.
Digging thru ToTok strings and classes we gain some potential insight into it’s possible origins:
/Users/jiangyaguang/Downloads/totok/YeeCall/Classes/TKSystemInfo.m /Users/jiangyaguang/Downloads/totok/YeeCall/Classes/Call/TKCallSessionViewController.m
patrick$ class-dump ToTok.app/ToTok @interface YeecallContact : NSManagedObject { } @interface YeecallReminder : NSManagedObject { } @interface YeeCallSecurityPolicy : AFSecurityPolicy { } As previously noted, we uncovered other ties to YeeCall. Based on these embedded strings it’s relatively clear that ToTok is largely composed of code from YeeCall. According to CrunchBase YeeCall is “a software company that has developed Yeecall messenger app for video & voice calling.” It is rather unsurprising that ToToks is simply based on existing code/an product (vs. written entirely from scratch).
It’s possible that “Breej Holding Ltd” (that “publisher” of the iOS app), simply contracted or licensed existing code from “YeeCall” to create the ToTok application. This would be a simple and efficient way to quickly create a new fully-featured application. This also explains the rather odd CFBundleLocalizations of
It’s more than likely that “Breej Holding Ltd” is not an actual iOS developer / publishing company:
“A technical analysis and interviews with computer security experts showed that the firm behind ToTok, Breej Holding, is most likely a front company affiliated with DarkMatter, an Abu Dhabi-based cyberintelligence and hacking firm where Emirati intelligence officials” -New York Times
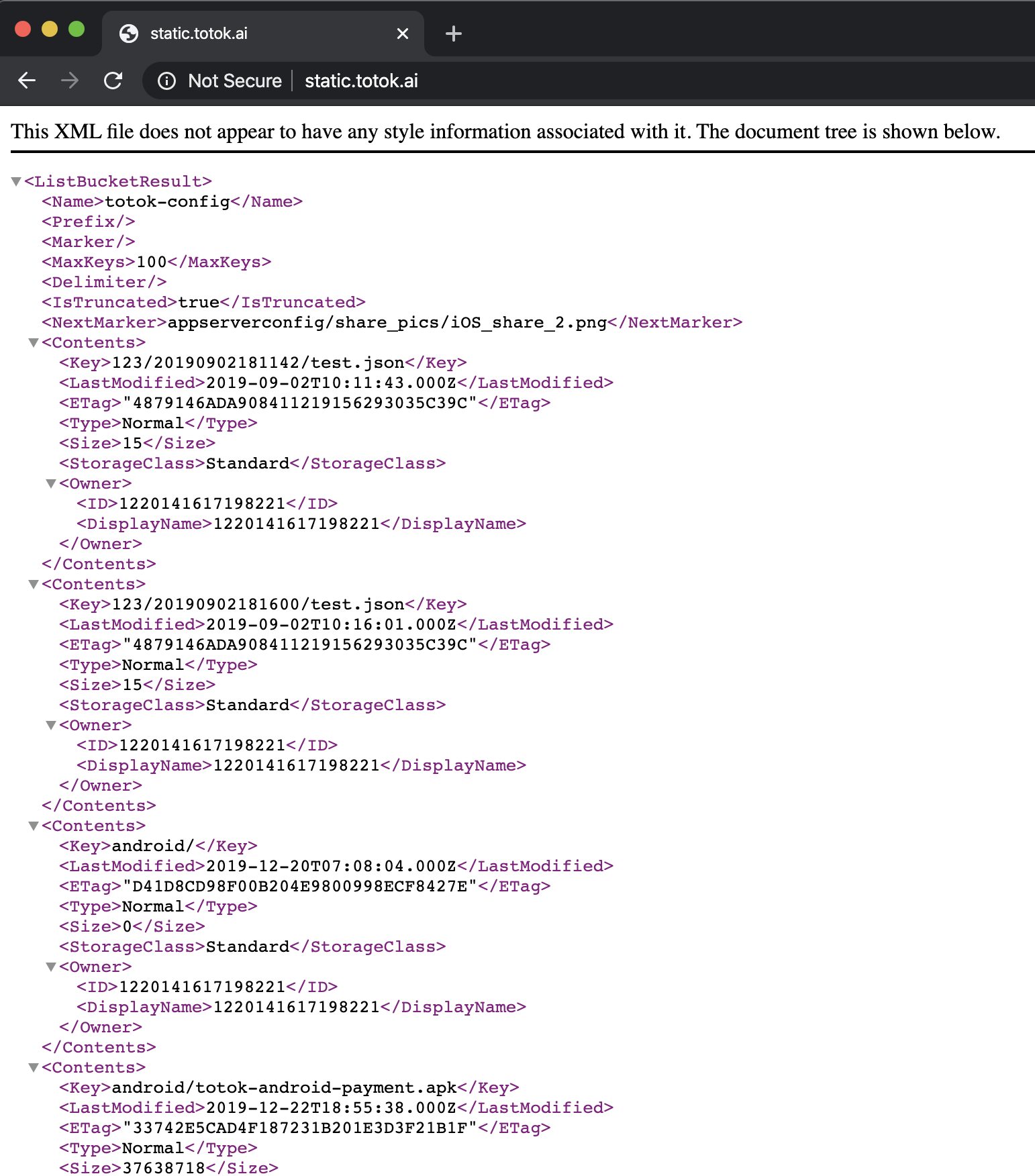
Other embedded strings, reveal static.totok.ai, the server which serves up static content for the app (images, icons, etc). The server appears to be misconfigured, and as such, browsing to it’s root reveals a listing of the all hosted files:
Conclusion
In this blog post, we triaged ToTok, an iOS application that the American intelligence community has claimed, was spy tool used by the United Arab Emirates government. 🙈
Our analysis showed that ToTok, simply does what it claims to do…and really nothing more. Assuming the claims that ToTok is actual designed to spy on it’s users, this “legitimace” functionality of the app, is really the genius of the whole mass surveillance operation: no exploits, no backdoors, no malware, …again, just “legitimate” functionality that likely afforded in-depth insight in a large percentage of the country’s population.
Think about it this way
…you’re a (rather surveillance-happy) foreign government who’d love to monitor your citizens.
In five easy steps:
- Ban popular apps such as WhatsApp, Skype
- Create a free alternative app that provides this banned functionality.
- Submit the app to the iOS app store, where it’s readily approved by Apple.
- Create fake reviews & social media posts that recommend the application.
- Wait as the citizens of your country readily embrace the app and it’s popularity soars.
…hooray! Now you have access to users’ address books, chats, location and more, in a completely “legitimate”, Apple-approved manner!
Such collection provides a sufficient “phase 1” (much like the NSA’s bulk metadata collection program) of a more comprehensive intelligence operation. Once you know who’s talking to whom, and perhaps even what they are saying, you can identify specific individuals of interest and target them with more advanced capabilities. This “phase 2” includes more traditional offensive cyber-operations, which are far more targeted, stealthy, and invasive. However, such a phase is far more expensive and difficult to scale and thus requires a sufficient “phase 1” component …like ToTok
from Hacker News https://ift.tt/394OFYg